Know What's
Exposed.
Before
Attackers Do.
See every exposed asset, open port, and risky service across your external footprint — automatically. No agents, no setup overhead, no blind spots.
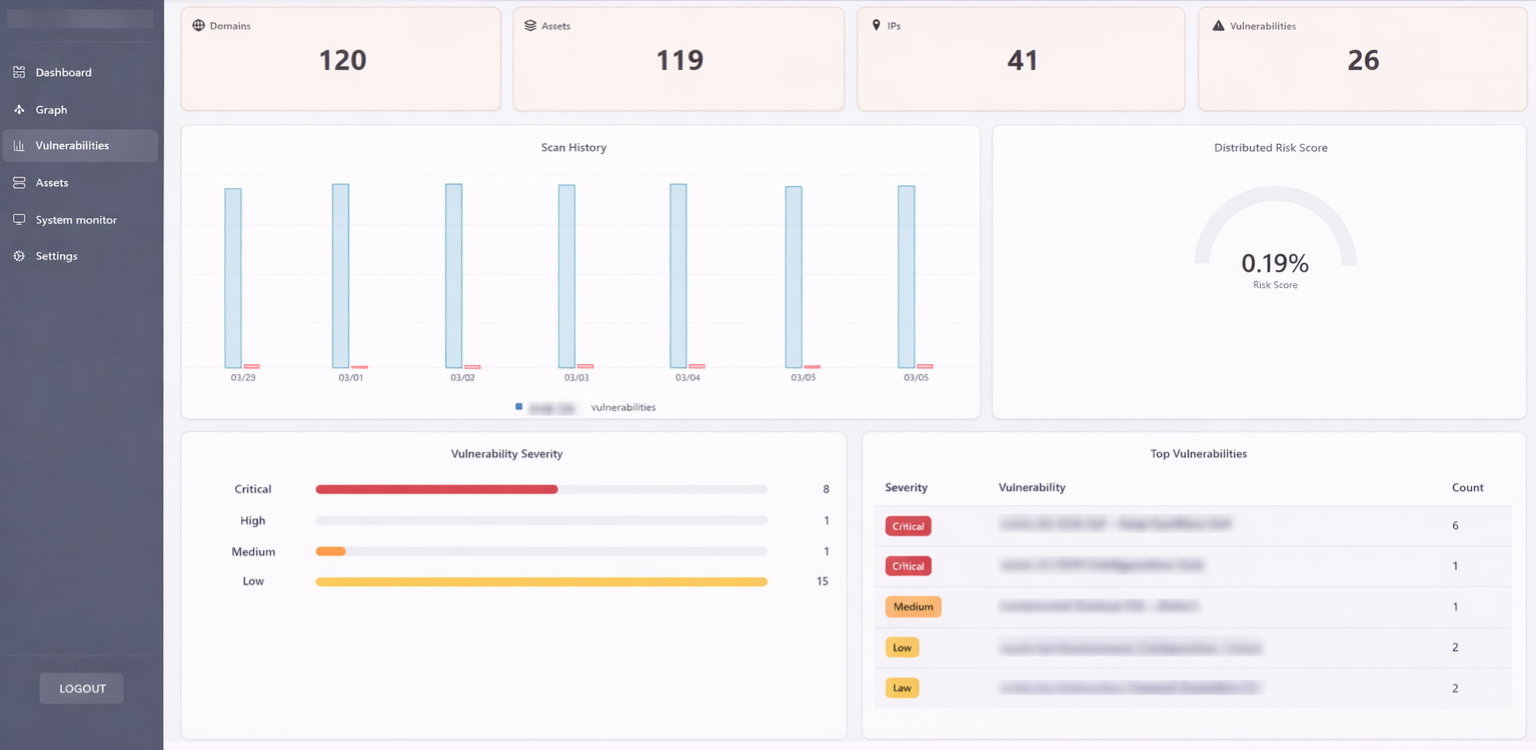
Vulnerabilities
26
Attack surfaces mapped
120+
Built for lean security teams. Continuous visibility from day one.
- 120+
- Organizations monitored
- Every 24h
- Automated scan frequency
- Zero
- Agents required
- < 5 min
- Time to first results
"Identified 3 forgotten subdomains exposing internal APIs within the first scan. We had no idea they were still live."
Continuous visibility. Real control.
What CyberSAM discovers for you
A practical platform to discover, map, and monitor your external digital footprint — no agents, no complexity.
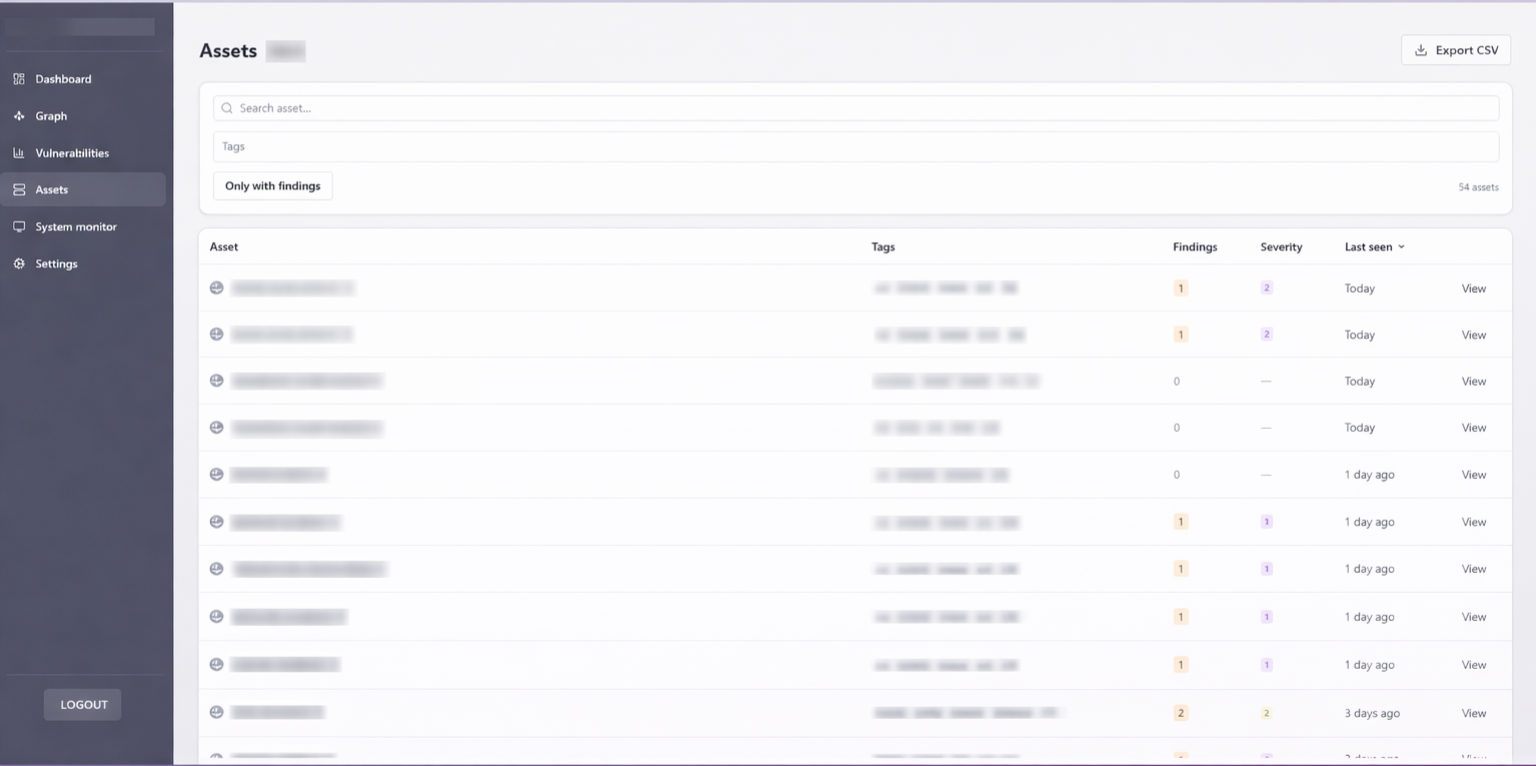
Full external inventory, always current
CyberSAM maps your entire external footprint continuously — no manual inventory, no missed assets, no stale data.
- Domains, subdomains & IPs
- Open ports & exposed services
- Technologies & fingerprints
- Historical exposure tracking
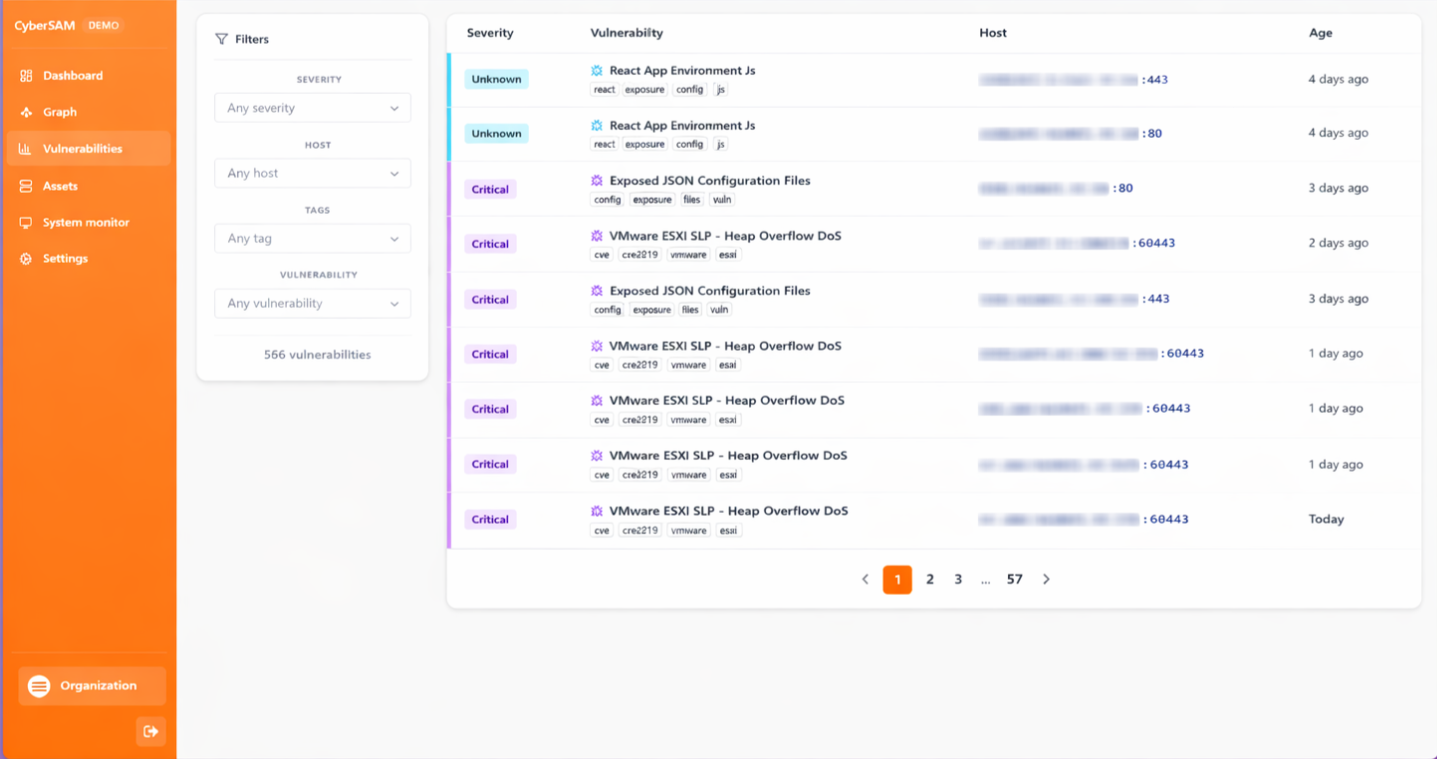
Find exposed assets faster
Identifies domains, subdomains, IPs, and open ports linked to your organization without any manual effort.
Spot risky services immediately
Scans exposed services for known vulnerabilities on a recurring basis — no analyst required to trigger a scan.
Reduce blind spots without agents
Works entirely externally — no software to install, no infrastructure changes, zero operational overhead.
Export findings and prove remediation
Generate exportable reports to share findings with stakeholders, track remediation progress, and satisfy audit requirements.
Visualize. Understand. Act.
The interactive graph of your attack surface
CyberSAM's dynamic graph lets you explore connections between domains, IPs, ports, and services. Understand how a misconfigured subdomain connects to an exposed service. Prioritize what actually matters.
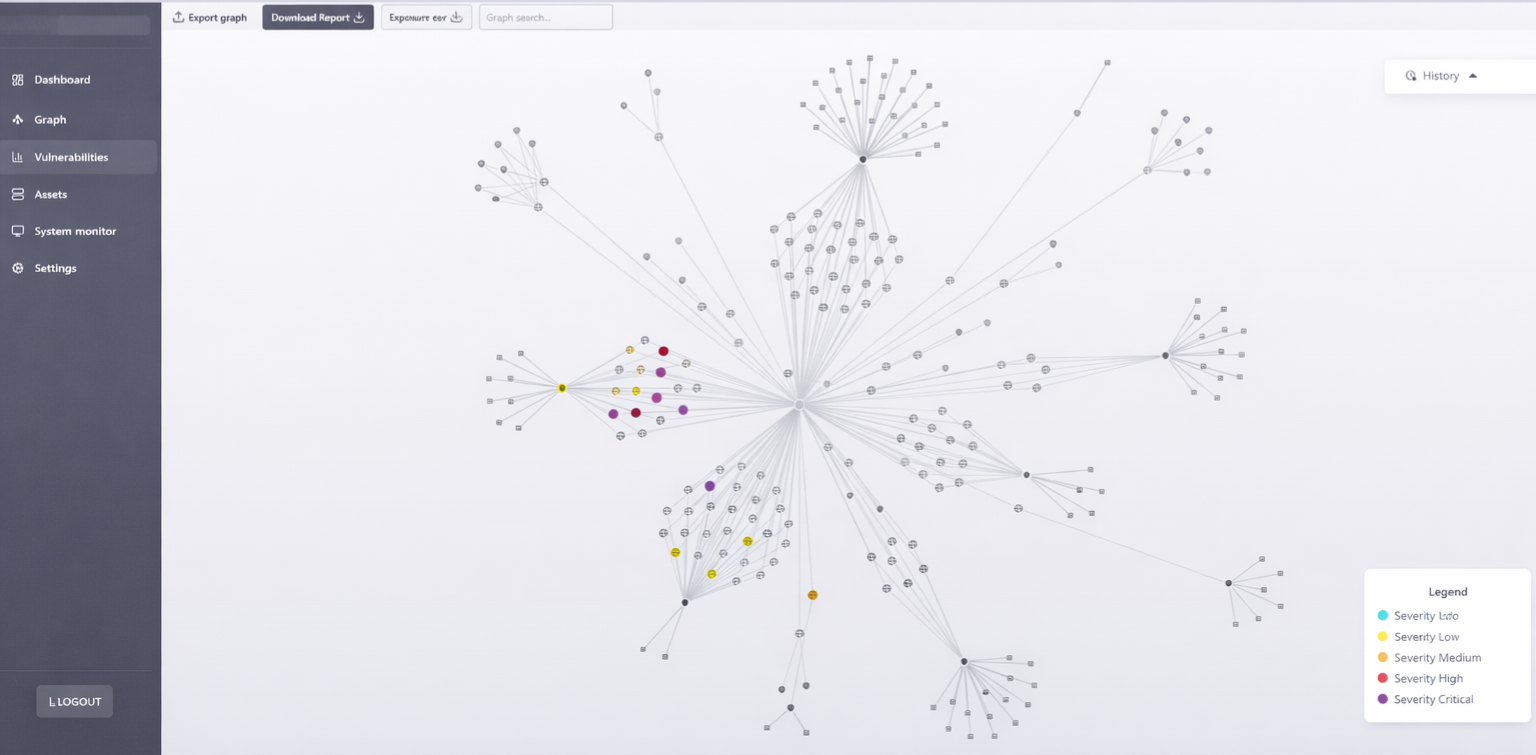
Understand what's reachable from the outside
The graph shows not just what exists, but how exposed nodes connect — so you can reason about reachability the same way an attacker would.
Prioritize what attackers would target first
Not just a list of what exists — an operational view of what's risky, reachable, and worth acting on before it becomes an incident.
Catch new exposure the moment it appears
New subdomains, newly open ports, newly deployed services — CyberSAM surfaces them on the next scan so your picture never goes stale.
Why teams choose CyberSAM
Built different from day one
Most ASM tools were built for large enterprise teams — months of onboarding, complex deployment, dedicated analysts. CyberSAM was built for fast-moving security teams that need visibility without the overhead.
No agent deployment
Works entirely from the outside — just like an attacker would. Zero changes to your infrastructure, zero operational overhead.
Fast time-to-value
Add a domain and get your first scan results in under 5 minutes. No lengthy onboarding, no professional services engagement.
Change detection built in
Know the moment a new service appears, a subdomain goes live, or an open port changes state — without manually checking anything.
Asset relationship mapping
Not just a list of assets — an interactive graph of how they connect. See which subdomain exposes which service and why it matters.
Built for lean teams
No dedicated security analyst required. CyberSAM surfaces what matters so a small team can act with the confidence of a large one.
"Identified 3 forgotten subdomains exposing internal APIs within the first scan. We had no idea they were still live."
— Security Lead, Italian Financial Services Firm
Use cases
Built for teams like yours
Security teams without a dedicated ASM program
Get continuous external visibility without building a full program from scratch.
MSSPs and security consultants
Add external footprint mapping to your service offering with zero infrastructure to manage.
Fast-growing companies
Stay ahead of exposure as your infrastructure scales — new assets get discovered automatically.
M&A due diligence and vendor risk
Map a target's external attack surface quickly for third-party evaluation — no access or cooperation needed.
Attack Surface Management made simple
How CyberSAM Works
Three simple steps to full visibility and control over your exposed infrastructure.
Add your domain
Enter your main domain — no agents to install, no infrastructure changes needed.
Discover and map
CyberSAM scans your entire footprint — subdomains, IPs, ports, and services — and maps them in an interactive graph.
Monitor & detect
Recurring scans surface vulnerabilities automatically. Track changes over time with no manual effort.